Attackers hijack npm maintainer account, steal crypto keys

- Attackers hijacked a dormant npm maintainer account and pushed three malicious node-ipc versions to steal credentials.
- The attacker re-registered the maintainer’s expired email domain and used npm’s password-reset flow to gain publish access.
- Any crypto dev or project that installed or auto-updated node-ipc during that window should audit dependencies and rotate all exposed secrets immediately.
Three poisoned versions of node-ipc went live on the npm registry on May 14, according to SlowMist. Attackers hijacked a dormant maintainer account and pushed code designed to siphon developer credentials, private keys, exchange API secrets, the works, straight out of .env files.
node-ipc is a popular Node.js package that lets different programs talk to each other on the same machine, or sometimes across a network.
SlowMist catches the breach
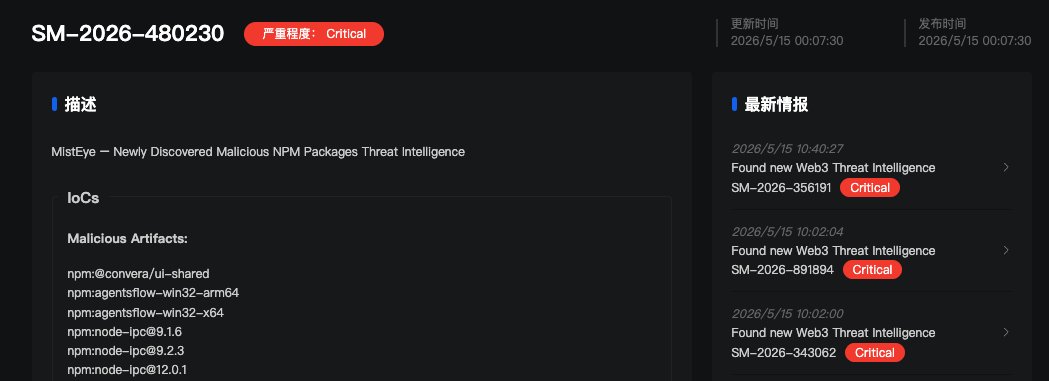
Blockchain security firm, SlowMist, spotted the breach through their MistEye threat intel system.
Versions 9.1.6, 9.2.3, and 12.0.1
MistEye found three malicious versions including:
- Version 9.1.6.
- Version 9.2.3.
- Version 12.0.1.
All of the above verions carried the same obfuscated 80 KB payload.
Node-ipc handles inter-process communication in Node.js. It basically helps Node.js programs send messages back and forth. Over 822,000 people download it each week.
Node-ipc is used all over the crypto space. It’s used in the tools developers use to build dApps, in the systems that automatically test and deploy code (CI/CD), and in everyday developer tools.
Each infected version had the same hidden malicious code bolted onto it. The moment any program loaded node-ipc, the code ran automatically.
Researchers at StepSecurity figured out how the attack happened. The original developer of node-ipc had an email address tied to the domain atlantis-software[.]net. However, the domain expired on January 10, 2025.
On May 7, 2026, the attacker bought the same domain through Namecheap, which gave them control of the developer’s old email. From there, they just hit “forgot password” on npm, reset it, and walked right in with full permission to publish new versions of node-ipc.
The real developer had no clue any of this was happening. The malicious versions stayed live for about two hours before removal.
The stealer looks for 90+ credential types
The embedded payload hunts for over 90 types of developer and cloud credentials. AWS tokens, Google Cloud and Azure secrets, SSH keys, Kubernetes configs, GitHub CLI tokens, all on the list.
For crypto devs, the malware specifically raids .env files. Those usually hold private keys, RPC node credentials, and exchange API secrets.
To sneak the stolen data out, the payload uses DNS tunneling. It basically hides the files inside normal-looking internet lookup requests. Most network security tools don’t catch that.
Security teams are saying any project that ran npm install or had auto-updated dependencies during that two hour window should assume compromise.
Immediate steps, per guidance from SlowMist:
- Check lock files for node-ipc versions 9.1.6, 9.2.3, or 12.0.1.
- Roll back to the last version you know is safe.
- Change every credential that might have leaked.
Supply chain attacks on npm have become a regular thing in 2026. Crypto projects get hit harder than most because stolen logins can be turned into stolen money fast.
The smartest crypto minds already read our newsletter. Want in? Join them.
FAQs
Which node-ipc versions carry the malware?
Versions 9.1.6, 9.2.3, and 12.0.1. SlowMist and StepSecurity both flagged them. All three had the same obfuscated payload that runs as soon as you load the package.
How did the attacker take over the maintainer account?
The original maintainer's email domain, atlantis-software[.]net, expired January 10, 2025. Attacker re-registered it through Namecheap on May 7, 2026, then used npm's password reset process to grab the account.
What does the stealer actually grab?
Over 90 types of credentials. AWS tokens, Google Cloud and Azure credentials, SSH keys, Kubernetes configs, GitHub CLI tokens, shell history files, and .env files, which often hold crypto private keys and exchange API secrets.

Randa Moses
Randa is a writer and editor specializing in technology. She graduated from the University of Bradford with a degree in Electrical and Electronics Engineering. She has worked at Forward Protocol, Amazix, and Cryptosomniac.
CRASH COURSE
- Which cryptocurrencies can make you money
- How to boost your security with a wallet (and which ones are actually worth using)
- Little-known investment strategies that the pros use
- How to get started investing in crypto (which exchanges to use, the best crypto to buy etc)