3 VS Code extensions stealing credentials for GitHub, VSX, and crypto wallets
- Cybersecurity firm Koi Security uncovers a new wave of the GlassWorm campaign, which hides malware in invisible Unicode code within VS Code extensions.
- The malware steals GitHub, Open VSX, and crypto wallet credentials, turning developer machines into proxy infrastructure and spreading through supply chains.
- GlassWorm uses the Solana blockchain as a command-and-control system, making the operation decentralized, resilient, and nearly impossible to shut down.
Developers will have to contend with a dormant turned active malicious code on Visual Studio Code (VS Code) extensions, which is believed to have compromised thousands of users by stealing credentials for GitHub, Open VSX, and cryptocurrency wallets.
Operation GlassWorm, first identified by cybersecurity firm Koi Security late last month, was created by a group hacking VS Code extensions distributed through both the Open VSX Registry and Microsoft’s Visual Studio Marketplace. The bad actors have reportedly been embedding invisible malicious code within legitimate-looking developer tools.
Koi security researchers say the campaign is mainly to harvest developer credentials like NPM tokens, GitHub logins, and Git credentials, to enable supply chain compromise and financial theft.
According to Koi’s analysis, the same malware has also targeted 49 different cryptocurrency wallet extensions, draining user funds and exfiltrating sensitive data to remote servers.
GlassWorm turns developer machines into criminals’ aid
As reported by Koi’s team blog article shared on several subreddits, the malicious extensions deploy SOCKS proxy servers and use the compromised developer systems to build up a criminal proxy network. In parallel, they install hidden VNC servers, giving attackers full remote access to victim machines without visible indicators.
Stolen GitHub and NPM credentials help the operators infect additional repositories and packages, and allow GlassWorm to propagate deeper into the software supply chain.
Open VSX confirmed it had identified and removed all known malicious extensions associated with the campaign on October 21, also revoking and rotating compromised tokens.
However, Koi Security’s new report indicates that GlassWorm has resurfaced, using a more advanced form of Unicode-based obfuscation to bypass detection systems.
According to the company, seven extensions were compromised again on October 17, amassing a combined 35,800 downloads. Koi’s telemetry also shows that ten infected extensions are currently active and publicly available, and distribute malware as of this writing.
“The attacker’s command-and-control infrastructure remains fully operational. Payload servers are still responding, and stolen credentials are being used to compromise new packages.”
CodeJoy malware is invincible, Koi security debunks
Koi’s risk analysis engine flagged an Open VSX extension called CodeJoy after version 1.8.3 exhibited “unusual behavioral changes.” CodeJoy looks like a legitimate developer productivity tool with hundreds of downloads, a clean codebase, and regular updates.
“When we opened the source code, we noticed a massive gap between lines two and seven,” Koi researchers said. “That’s not empty space, it’s malicious code encoded in unprintable Unicode characters that don’t render in your code editor.”
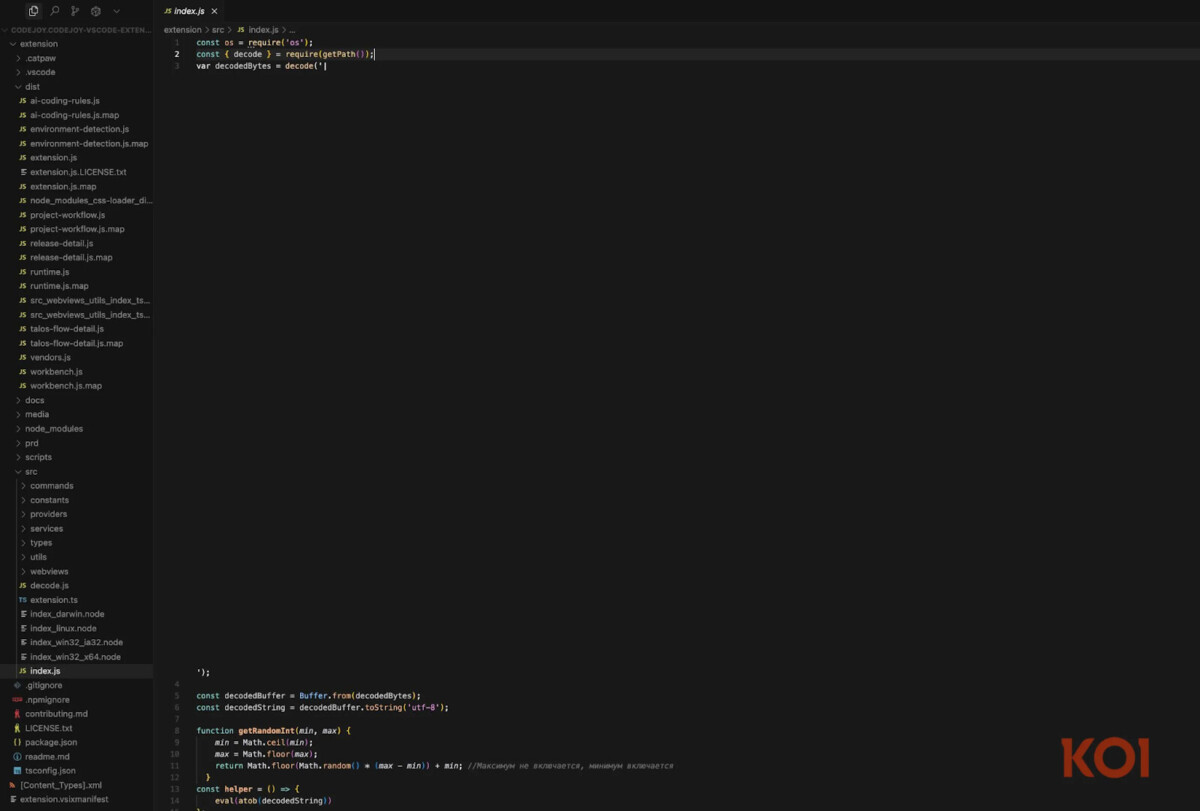
The attackers used invincible Unicode variation selectors that make the malicious payload invisible to the human eye. Static analysis tools and manual code reviews saw nothing unusual, yet the JavaScript interpreter executed the hidden commands flawlessly.
When decoded, the invisible characters revealed a second-stage payload mechanism, one that Koi researchers discovered uses the Solana blockchain as its command-and-control (C2) infrastructure.
“The attacker is using a public blockchain, which is immutable, decentralized, and censorship-resistant, as their C2 channel,” Koi explained.
The malware scans the Solana network for transactions from a hardcoded wallet address. Upon finding one, it reads the memo field, where arbitrary text can be attached to transactions. Inside that memo field lies a JSON object containing a base64-encoded link to download the next-stage payload.
A Solana transaction from October 15 displayed in Koi’s analysis contained data that was decoded to a URL hosting the active location for downloading the next stage of the malware.
An attacker can rotate payloads by posting a new Solana transaction for fractions of a cent, updating all infected extensions that query the blockchain for new instructions.
Per Koi, even if defenders block one payload URL, the attacker can issue another transaction faster than it takes to bring one down.
“It’s like playing whack-a-mole with infinite moles,” a Koi researcher noted.
Koi Security members Idan Dardikman, Yuval Ronen, and Lotan Sery confirmed that the threat actor has posted fresh Solana transactions containing new command endpoints as recently as this week.
Your bank is using your money. You’re getting the scraps. Watch our free video on becoming your own bank
Disclaimer. The information provided is not trading advice. Cryptopolitan.com holds no liability for any investments made based on the information provided on this page. We strongly recommend independent research and/or consultation with a qualified professional before making any investment decisions.
CRASH COURSE
- Which cryptocurrencies can make you money
- How to boost your security with a wallet (and which ones are actually worth using)
- Little-known investment strategies that the pros use
- How to get started investing in crypto (which exchanges to use, the best crypto to buy etc)















