- Security firm Socket has uncovered nine malicious NuGet packages designed to activate in 2027 and 2028, targeting databases and industrial control systems.
- The most dangerous package, Sharp7Extend, mimics the legitimate Sharp7 library to infiltrate Siemens PLC environments with delayed sabotage mechanisms.
- Investigators also linked the campaign to a possible Chinese actor and uncovered a related IIS server attack exploiting decades-old ASP.NET vulnerabilities.
Two years ago, an account with the name “shanhai666” uploaded nine malicious NuGet packages. This launched a complicated software supply-chain attack.
According to supply-chain security firm Socket, the packages have been collectively downloaded 9,488 times. In addition, specific triggers are set for August 2027 and November 2028.
Socket’s team member, Kush Pandya, discovered the threat actor behind the campaign that published a total of 12 packages. Nine of the packages contain harmful routines, while three are fully functional implementations disguising the rest as “credible.”
Pandya believes the hacker used legitimate libraries together with the malicious ones to trick developers into installing the packages without detecting anomalies during routine testing.
“Legitimate functionality masks the ~20-line malicious payload buried in thousands of lines of legitimate code, and delays discovery since even after activation, crashes appear as random bugs rather than systematic attacks,” he wrote in a November 6 report.
9 NuGet hidden threats in legitimate code
The nine identified malicious packages could affect all three major database providers used in .NET applications: Microsoft SQL Server, PostgreSQL, and SQLite. One package, Sharp7Extend, specifically targets industrial PLCs used in manufacturing and process automation.
Socket’s research propounded that the database could be vulnerable to a dual-purpose supply-chain attack threatening software development and critical infrastructure operations.
Pandya coined package Sharp7Extend as the most dangerous of the malicious packages, being a typosquat of the legitimate Sharp7 library .NET implementation for communicating with Siemens S7 programmable logic controllers.
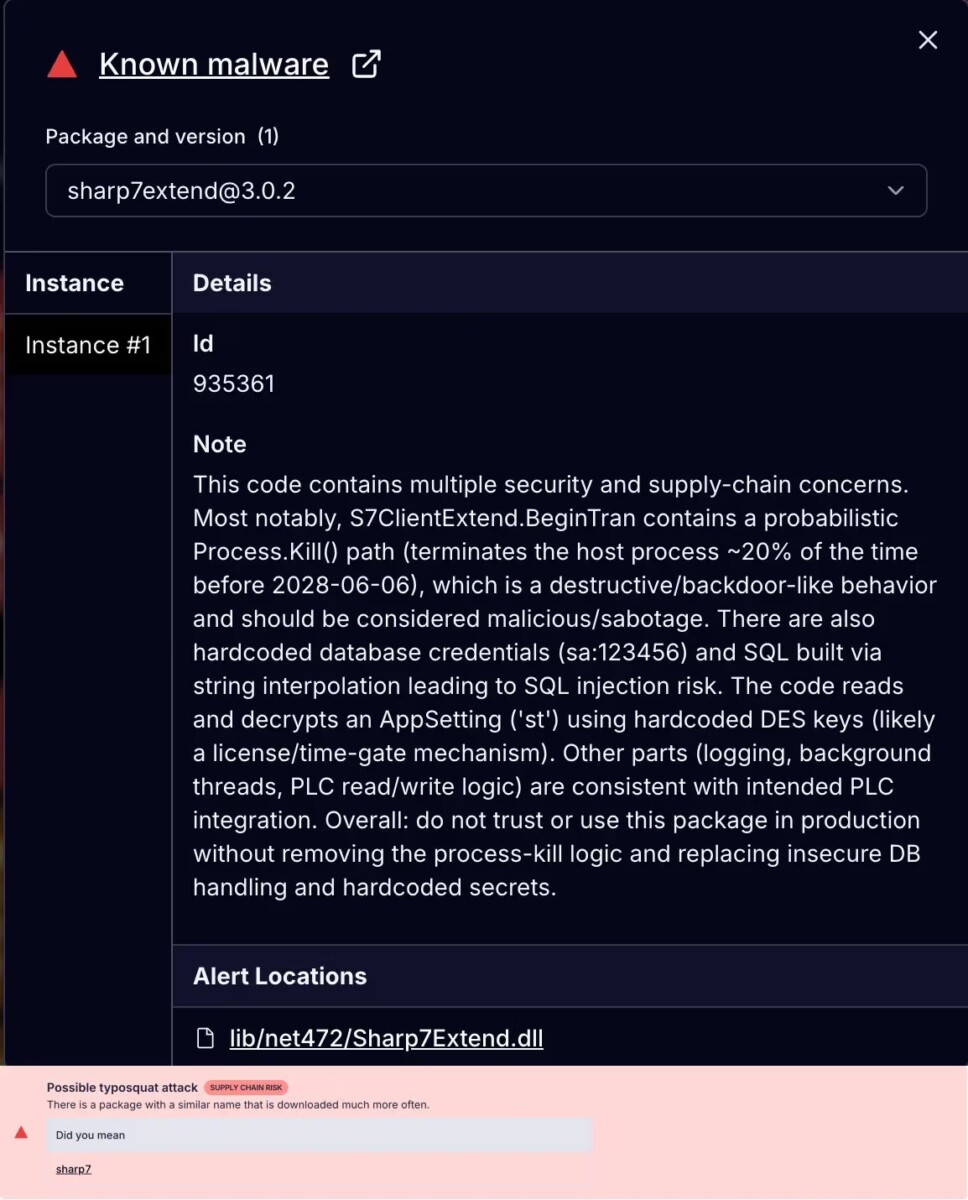
Appending “Extend” to the trusted name could help the malicious package “accidentally” install code through automation engineers searching for Sharp7 improvements. The package bundles the full unmodified Sharp7 library with its malicious payload. Standard PLC communication may appear as if it’s working as expected during testing, but the embedded malware is masked.
“Sharp7Extend targets industrial PLCs with dual sabotage mechanisms: immediate random process termination and silent write failures that begin 30-90 minutes after installation,” the security researcher said.
The malicious packages use C# extension methods to add dangerous code to database and PLC operations without changing the original code. For database packages, an .Exec() method is added to command types, while Sharp7Extend adds a .BeginTran() method to S7Client objects.
The extensions run automatically every time an application does a PLC action or a query. After the trigger date, the malware makes a random number between 1 and 100.
If the number exceeds 80, which there’s a 20% probability it will actually happen, the package immediately kills the running process using Process.GetCurrentProcess().Kill(). An abrupt termination then occurs without warnings or log entries that could seem like network instability, hardware faults, or other “non alarming” system errors.
Sharp7Extend also implements delayed write corruption through a timer that sets a 30–90 minute grace period. After the grace period, a filter method called ResFliter.fliter() begins silently failing write operations 80% of the time.
Methods affected include WriteDBSingleByte, WriteDBSingleInt, and WriteDBSingleDInt. Operations appear successful while data is not actually written to the PLC.
Timer set for August 2027 to November 2028
Socket security’s report said certain database-focused packages in the campaign’s crossroads, including MCDbRepository, are slated to execute their payload on August 8, 2027. SqlUnicornCore and SqlUnicornCoreTest could likely go active on November 29, 2028.
“This staggered approach gives the threat actor a longer window to collect victims before the delayed-activation malware triggers, while immediately disrupting industrial control systems,” Pandya explained.
Socket’s investigation found that the name “shanhai666” and portions of the source code is of Chinese origin.
In September, cybersecurity analysts uncovered code on Microsoft Internet Information Services (IIS) servers that had been exploiting vulnerabilities since 2003. The operation involves malicious IIS modules used for remote command execution and search engine optimization (SEO) fraud.
The smartest crypto minds already read our newsletter. Want in? Join them.
Disclaimer. The information provided is not trading advice. Cryptopolitan.com holds no liability for any investments made based on the information provided on this page. We strongly recommend independent research and/or consultation with a qualified professional before making any investment decisions.
CRASH COURSE
- Which cryptocurrencies can make you money
- How to boost your security with a wallet (and which ones are actually worth using)
- Little-known investment strategies that the pros use
- How to get started investing in crypto (which exchanges to use, the best crypto to buy etc)