TAC declares $2.8M exploit as white hat incident after hacker refunds loot
- TAC lost $2.8 million in an exploit targeting the TON side of its cross-chain bridge, affecting USDT, BLUM, and tsTON assets.
- The team offered the attacker a bounty to return the funds to a designated multisig wallet in exchange for classifying the incident as white hat.
- The exploit comes during a month already marked by multiple crypto security breaches and follows April’s $651 million in sector-wide losses.
TAC, a cross-chain protocol that has marketed itself as a bridge between TON and Ethereum, has now reclassified its $2.8 million exploit from May 12 as a white hat event, after the hacker apparently took the team up on its offer to keep 10% of the “moved” funds in exchange for returning the rest to its multisig wallets.
According to TAC’s disclosures of the event, the exploit targeted the TON side of its cross-chain layer, draining funds across USDT, BLUM, and tsTON. TAC said the vulnerability was isolated to native TON Jettons bridged from the TON network, and that the TAC token itself, TON, and all ERC-20 tokens were unaffected.
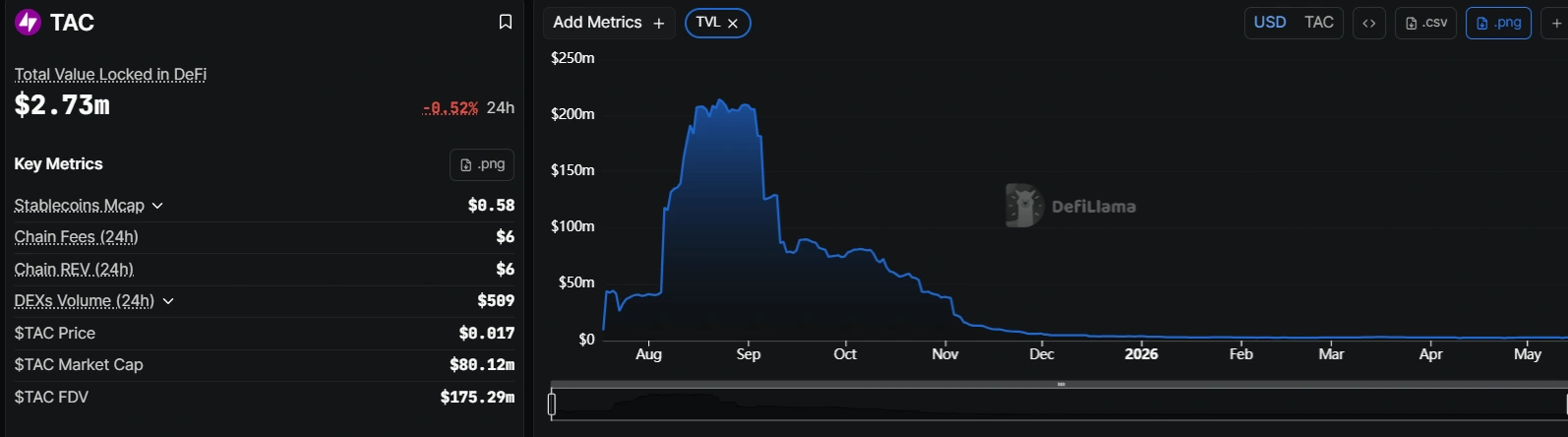
The TAC token has taken a beating since the exploit, with price dropping more than 21% over the last week. Market cap is down to $79 million from over $91 million before the May 12 disclosure of the hack.

TAC’s total value locked sits at approximately $2.74 million as of May 14, per DefiLlama, meaning the $2.8 million exploit roughly equaled the protocol’s entire TVL.
How did the TAC Protocol exploit happen?
TAC first disclosed that it had been hacked on May 12. The message from the team on X claimed that it had paused the bridge after receiving reports from security partners. The team quickly moved to allay fears by insisting that the issue was limited in scope, affecting only a subset of bridged assets rather than the protocol’s broader infrastructure.
As for how it would handle the coming days, the TAC Protocol team said: “Our focus is on making users whole and fully restoring bridge liquidity through a legally structured sale of Foundation’s TAC token treasury reserves.”
By May 14, TAC had positive news to share. The team said that after the exploiter took its offer to return funds to the designated multisig wallet on Ethereum and a corresponding address on TON, it came to the decision not to pursue litigation, a decision that it coordinated with its security partners and law enforcement.
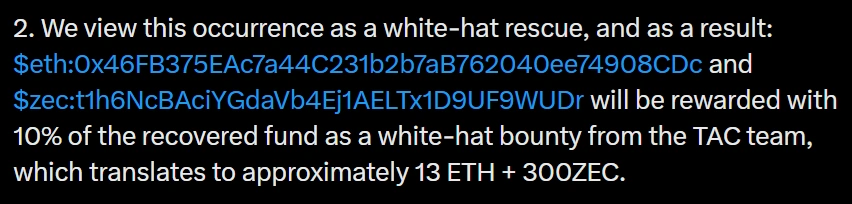
With the refunds, the TAC Protocol hack quickly went from exploit to white hat incident, with a 10% bounty offered up as incentive, which comes to about 13 ETH + 300ZEC.
It is standard practice in Web3 to offer hackers a percentage of stolen funds in exchange for returning the majority of the loot. Transit Finance took a page from that book earlier this week after it lost $1.88 million from a deprecated TRON smart contract. The team sent an on-chain message to its attacker offering a percentage of stolen funds as a bug bounty in exchange for cooperation, with a 48-hour response window.
Hackers drag cross-chain protocols through the wringer
TAC’s exploit adds to a pattern of bridge and cross-chain vulnerabilities in early May 2026. Transit Finance attributed its breach to a contract that had been deprecated since 2022 but still held exploitable code. Security firm GoPlus Security flagged two private key compromises on May 12 totaling $238,000, and blockchain security company Blockaid identified a $456,000 exploit on Aurellion Labs’ uninitialized Diamond proxy contract on Arbitrum, according to Cryptopolitan’s reporting.
The losses follow a rough April. CertiK reported approximately $651 million lost to exploits across the sector that month, the highest since March 2022, when excluding the Bybit incident in February 2025. The KelpDAO bridge exploit ($293 million) and Drift Protocol hack ($285 million) accounted for most of April’s damage.
May’s individual incidents are smaller by comparison, but the frequency suggests the underlying conditions that enabled April’s record losses have not been addressed.
TAC Protocol’s bridge remains paused. The team has not disclosed a timeline for resuming operations, but it said it will direct the remaining balance, minus the white hat bounty, to its multisig wallets.
The smartest crypto minds already read our newsletter. Want in? Join them.
Disclaimer. The information provided is not trading advice. Cryptopolitan.com holds no liability for any investments made based on the information provided on this page. We strongly recommend independent research and/or consultation with a qualified professional before making any investment decisions.
Hannah Collymore
Hannah is a writer and editor with nearly a decade of blog writing and event reporting experience. She graduated from Arcadia university where she studied business administration. She now works with Cryptopolitan, where she contributes to reporting on the latest developments in the cryptocurrency, gaming, and AI industries.
CRASH COURSE
- Which cryptocurrencies can make you money
- How to boost your security with a wallet (and which ones are actually worth using)
- Little-known investment strategies that the pros use
- How to get started investing in crypto (which exchanges to use, the best crypto to buy etc)