Brazilian trojan hijacks WhatsApp to spread crypto phishing

- TCLBANKER is a Brazilian banking trojan that monitors 59 banking and crypto domains.
- The malware spreads by hijacking victims’ WhatsApp Web sessions and Outlook accounts to send phishing messages to their contacts.
- Brazilian crypto and fintech users are the primary targets.
Security researchers from Elastic Security Labs have discovered a new Brazilian banking trojan named TCLBANKER. When it infects a machine, it takes over the victim’s WhatsApp and Outlook accounts and sends phishing messages to their contacts.
The campaign is labeled as REF3076. Based on common infrastructure and code patterns, researchers have linked the TCLBANKER to the previously known malware family MAVERICK/SORVEPOTEL.
Trojan spreads through an AI prompt builder
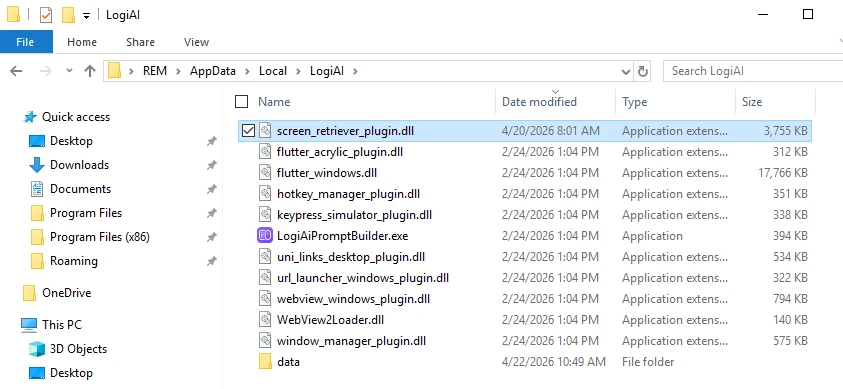
Elastic Security Labs says the malware comes as a trojanized installer for Logi AI Prompt Builder, which is a real signed Logitech app. The installer comes in a ZIP file and uses DLL sideloading to run a malicious file that looks like a Flutter plugin.
Once loaded, the trojan deploys two .NET Reactor-protected payloads. One is a banking module and the other is a worm module built for self-propagation.
After loading, the trojan deploys two .NET Reactor-protected payloads. One is a banking module, and the other is a worm module that can spread itself.
Anti-analysis checks block researchers
There are three parts that make up the fingerprint that TCLBANKER’s loader builds.
- Anti-debugging checks.
- Disk and memory information.
- Language settings.
The fingerprint generates the decryption keys for the embedded payload. If something seems wrong, such as a debugger attached, a sandbox environment, or low disk space, the decryption produces garbage, and the malware stops silently.
The loader also patches Windows telemetry functions to blind security tools. It creates direct syscall trampolines to avoid user-mode hooks.
A watchdog is always looking for analysis software such as x64dbg, Ghidra, dnSpy, IDA Pro, Process Hacker, and Frida. If any of these tools is found, the payload stops working.
Banking module activates only on Brazilian computers
The banking module activates on computers located in Brazil. There’s a minimum of two geofencing checks that look at region code, time zone, system locale, and keyboard layout.
The malware reads the active browser URL bar using Windows UI Automation. It works across many browsers like Chrome, Firefox, Edge, Brave, Opera, and Vivaldi, and it monitors active URL/URLs every second.
The malware then matches the URL to a list of 59 encrypted URLs. This list has links to crypto, banks, and fintech websites in Brazil.
When a victim visits one of the targeted websites, the malware opens a WebSocket to a remote server. The hacker then gets full remote control of the computer.
Once access is granted, the hacker uses an overlay that puts a borderless, topmost window over every monitor. The overlay is not visible in screenshots, and victims can’t share what they see with others.
The hacker’s overlay has three templates:
- A credential harvesting form with a fake Brazilian phone number.
- A Fake Windows Update progress screen.
- A “vishing wait screen” that keeps victims busy.
Malicious bots spread the Brazilian trojan on WhatsApp and Outlook
The second payload spreads TCLBANKER to new victims through two ways:
- WhatsApp web app.
- Outlook inboxes/accounts.
The WhatsApp bot looks for active WhatsApp Web sessions in Chromium browsers by locating the app’s local database directories.
The bot clones the browser profile, then launches a headless Chromium instance. “A headless browser is a web browser without a graphical user interface,” according to Wikipedia. It then injects JavaScript to bypass bot detection and harvests the victim’s contacts.
At the end, the bot sends phishing messages containing the TCLBANKER installer to the victim’s contacts.
The Outlook bot connects through Component Object Model (COM) automation. COM automation lets a program control another program.
The bot takes email addresses from the Contacts folder and the inbox history, then it sends phishing emails using the victim’s account.
The emails have the subject line “NFe disponível para impressão,” which means in English, “Electronic Invoice Available for Printing”. It links to a phishing domain impersonating a Brazilian ERP platform.
Since the emails are sent from real accounts, they are more likely to bypass spam filters.
Last week, Cryptopolitan reported that researchers identified four Android trojans targeting +800 crypto, banking, and social media apps with fake login overlays.
In another report, a malware called StepDrainer has been draining wallets across +20 blockchain networks using fake Web3 wallet connection interfaces.
The smartest crypto minds already read our newsletter. Want in? Join them.
FAQs
What is TCLBANKER and how does it spread?
TCLBANKER is a Brazilian banking trojan delivered through a trojanized Logitech installer. It hijacks victims' WhatsApp Web sessions and Outlook email accounts to send phishing messages to their contacts.
Which crypto platforms does TCLBANKER target?
The trojan monitors an encrypted list of 59 Brazilian banking, fintech, and cryptocurrency domains. It activates a remote-control session when a victim visits any of those sites in their browser.
How does TCLBANKER avoid detection by security researchers?
The malware generates an environment fingerprint from anti-debugging checks, system hardware, and language settings, then uses that fingerprint to decrypt its payload. If any check fails, the payload never decrypts and execution stops silently.
Disclaimer. The information provided is not trading advice. Cryptopolitan.com holds no liability for any investments made based on the information provided on this page. We strongly recommend independent research and/or consultation with a qualified professional before making any investment decisions.
CRASH COURSE
- Which cryptocurrencies can make you money
- How to boost your security with a wallet (and which ones are actually worth using)
- Little-known investment strategies that the pros use
- How to get started investing in crypto (which exchanges to use, the best crypto to buy etc)















